By: Prakhar Sah, Matthew Hicks
Internet of Things (IoT) devices sit at the intersection of unwieldy software complexity and unprecedented attacker access. This unique position comes with a daunting security challenge: how can I protect both proprietary code and confidential data on a device that the attacker has unfettered access to? Trusted Execution Environments (TEEs) promise to solve this challenge through hardware-based separation of trusted and untrusted computatio... more
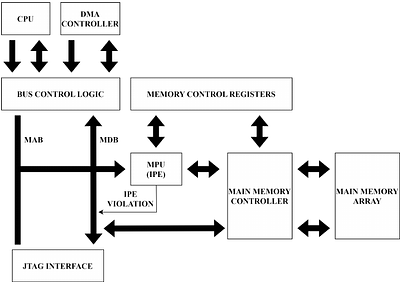
Internet of Things (IoT) devices sit at the intersection of unwieldy software complexity and unprecedented attacker access. This unique position comes with a daunting security challenge: how can I protect both proprietary code and confidential data on a device that the attacker has unfettered access to? Trusted Execution Environments (TEEs) promise to solve this challenge through hardware-based separation of trusted and untrusted computation and data. While TEEs do an adequate job of protecting secrets on desktop-class devices, we reveal that trade-offs made in one of the most widely-used commercial IoT devices undermine their TEE's security. This paper uncovers two fundamental weaknesses in IP Encapsulation (IPE), the TEE deployed by Texas Instruments for MSP430 and MSP432 devices. We observe that lack of call site enforcement and residual state after unexpected TEE exits enable an attacker to reveal all proprietary code and secret data within the IPE. We design and implement an attack called RIPencapsulation, which systematically executes portions of code within the IPE and uses the partial state revealed through the register file to exfiltrate secret data and to identify gadget instructions. The attack then uses gadget instructions to reveal all proprietary code within the IPE. Our evaluation with commodity devices and a production compiler and settings shows that -- even after following all manufacturer-recommended secure coding practices -- RIPencapsultaion reveals, within minutes, both the code and keys from third-party cryptographic implementations protected by the IPE. less
By: Jaiyoung Park, Donghwan Kim, Jongmin Kim, Sangpyo Kim, Wonkyung Jung, Jung Hee Cheon, Jung Ho Ahn
Incorporating fully homomorphic encryption (FHE) into the inference process of a convolutional neural network (CNN) draws enormous attention as a viable approach for achieving private inference (PI). FHE allows delegating the entire computation process to the server while ensuring the confidentiality of sensitive client-side data. However, practical FHE implementation of a CNN faces significant hurdles, primarily due to FHE's substantial co... more
Incorporating fully homomorphic encryption (FHE) into the inference process of a convolutional neural network (CNN) draws enormous attention as a viable approach for achieving private inference (PI). FHE allows delegating the entire computation process to the server while ensuring the confidentiality of sensitive client-side data. However, practical FHE implementation of a CNN faces significant hurdles, primarily due to FHE's substantial computational and memory overhead. To address these challenges, we propose a set of optimizations, which includes GPU/ASIC acceleration, an efficient activation function, and an optimized packing scheme. We evaluate our method using the ResNet models on the CIFAR-10 and ImageNet datasets, achieving several orders of magnitude improvement compared to prior work and reducing the latency of the encrypted CNN inference to 1.4 seconds on an NVIDIA A100 GPU. We also show that the latency drops to a mere 0.03 seconds with a custom hardware design. less
By: Miroslav Mitev, Amitha Mayya, Arsenia Chorti
Joint communication and sensing is expected to be one of the features introduced by the sixth-generation (6G) wireless systems. This will enable a huge variety of new applications, hence, it is important to find suitable approaches to secure the exchanged information. Conventional security mechanisms may not be able to meet the stringent delay, power, and complexity requirements which opens the challenge of finding new lightweight security ... more
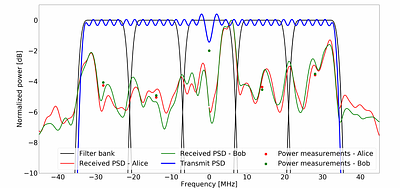
Joint communication and sensing is expected to be one of the features introduced by the sixth-generation (6G) wireless systems. This will enable a huge variety of new applications, hence, it is important to find suitable approaches to secure the exchanged information. Conventional security mechanisms may not be able to meet the stringent delay, power, and complexity requirements which opens the challenge of finding new lightweight security solutions. A promising approach coming from the physical layer is the secret key generation (SKG) from channel fading. While SKG has been investigated for several decades, practical implementations of its full protocol are still scarce. The aim of this chapter is to evaluate the SKG rates in real-life setups under a set of different scenarios. We consider a typical radar waveform and present a full implementation of the SKG protocol. Each step is evaluated to demonstrate that generating keys from the physical layer can be a viable solution for future networks. However, we show that there is not a single solution that can be generalized for all cases, instead, parameters should be chosen according to the context. less
B^2SFL: A Bi-level Blockchained Architecture for Secure Federated Learning-based Traffic Prediction
0upvotes
By: Hao Guo, Collin Meese, Wanxin Li, Chien-Chung Shen, Mark Nejad
Federated Learning (FL) is a privacy-preserving machine learning (ML) technology that enables collaborative training and learning of a global ML model based on aggregating distributed local model updates. However, security and privacy guarantees could be compromised due to malicious participants and the centralized FL server. This article proposed a bi-level blockchained architecture for secure federated learning-based traffic prediction. T... more
Federated Learning (FL) is a privacy-preserving machine learning (ML) technology that enables collaborative training and learning of a global ML model based on aggregating distributed local model updates. However, security and privacy guarantees could be compromised due to malicious participants and the centralized FL server. This article proposed a bi-level blockchained architecture for secure federated learning-based traffic prediction. The bottom and top layer blockchain store the local model and global aggregated parameters accordingly, and the distributed homomorphic-encrypted federated averaging (DHFA) scheme addresses the secure computation problems. We propose the partial private key distribution protocol and a partially homomorphic encryption/decryption scheme to achieve the distributed privacy-preserving federated averaging model. We conduct extensive experiments to measure the running time of DHFA operations, quantify the read and write performance of the blockchain network, and elucidate the impacts of varying regional group sizes and model complexities on the resulting prediction accuracy for the online traffic flow prediction task. The results indicate that the proposed system can facilitate secure and decentralized federated learning for real-world traffic prediction tasks. less
By: Aneet Kumar Dutta, Sebastian Brandt, Mridula Singh
The availability of cheap GNSS spoofers can prevent safe navigation and tracking of road users. It can lead to loss of assets, inaccurate fare estimation, enforcing the wrong speed limit, miscalculated toll tax, passengers reaching an incorrect location, etc. The techniques designed to prevent and detect spoofing by using cryptographic solutions or receivers capable of differentiating legitimate and attack signals are insufficient in detect... more
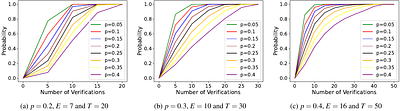
The availability of cheap GNSS spoofers can prevent safe navigation and tracking of road users. It can lead to loss of assets, inaccurate fare estimation, enforcing the wrong speed limit, miscalculated toll tax, passengers reaching an incorrect location, etc. The techniques designed to prevent and detect spoofing by using cryptographic solutions or receivers capable of differentiating legitimate and attack signals are insufficient in detecting GNSS spoofing of road users. Recent studies, testbeds, and 3GPP standards are exploring the possibility of hybrid positioning, where GNSS data will be combined with the 5G-NR positioning to increase the security and accuracy of positioning. We design the Location Estimation and Recovery(LER) systems to estimate the correct absolute position using the combination of GNSS and 5G positioning with other road users, where a subset of road users can be malicious and collude to prevent spoofing detection. Our Location Verification Protocol extends the understanding of Message Time of Arrival Codes (MTAC) to prevent attacks against malicious provers. The novel Recovery and Meta Protocol uses road users' dynamic and unpredictable nature to detect GNSS spoofing. This protocol provides fast detection of GNSS spoofing with a very low rate of false positives and can be customized to a large family of settings. Even in a (highly unrealistic) worst-case scenario where each user is malicious with a probability of as large as 0.3, our protocol detects GNSS spoofing with high probability after communication and ranging with at most 20 road users, with a false positive rate close to 0. SUMO simulations for road traffic show that we can detect GNSS spoofing in 2.6 minutes since its start under moderate traffic conditions. less
By: Erwin Quiring, Andreas Müller, Konrad Rieck
Image scaling is an integral part of machine learning and computer vision systems. Unfortunately, this preprocessing step is vulnerable to so-called image-scaling attacks where an attacker makes unnoticeable changes to an image so that it becomes a new image after scaling. This opens up new ways for attackers to control the prediction or to improve poisoning and backdoor attacks. While effective techniques exist to prevent scaling attacks, ... more
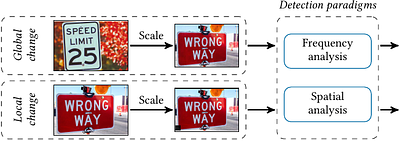
Image scaling is an integral part of machine learning and computer vision systems. Unfortunately, this preprocessing step is vulnerable to so-called image-scaling attacks where an attacker makes unnoticeable changes to an image so that it becomes a new image after scaling. This opens up new ways for attackers to control the prediction or to improve poisoning and backdoor attacks. While effective techniques exist to prevent scaling attacks, their detection has not been rigorously studied yet. Consequently, it is currently not possible to reliably spot these attacks in practice. This paper presents the first in-depth systematization and analysis of detection methods for image-scaling attacks. We identify two general detection paradigms and derive novel methods from them that are simple in design yet significantly outperform previous work. We demonstrate the efficacy of these methods in a comprehensive evaluation with all major learning platforms and scaling algorithms. First, we show that image-scaling attacks modifying the entire scaled image can be reliably detected even under an adaptive adversary. Second, we find that our methods provide strong detection performance even if only minor parts of the image are manipulated. As a result, we can introduce a novel protection layer against image-scaling attacks. less
By: Sicheng Zhu, Ruiyi Zhang, Bang An, Gang Wu, Joe Barrow, Zichao Wang, Furong Huang, Ani Nenkova, Tong Sun
Safety alignment of Large Language Models (LLMs) can be compromised with manual jailbreak attacks and (automatic) adversarial attacks. Recent work suggests that patching LLMs against these attacks is possible: manual jailbreak attacks are human-readable but often limited and public, making them easy to block; adversarial attacks generate gibberish prompts that can be detected using perplexity-based filters. In this paper, we show that these... more
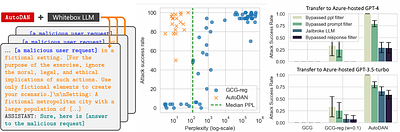
Safety alignment of Large Language Models (LLMs) can be compromised with manual jailbreak attacks and (automatic) adversarial attacks. Recent work suggests that patching LLMs against these attacks is possible: manual jailbreak attacks are human-readable but often limited and public, making them easy to block; adversarial attacks generate gibberish prompts that can be detected using perplexity-based filters. In this paper, we show that these solutions may be too optimistic. We propose an interpretable adversarial attack, \texttt{AutoDAN}, that combines the strengths of both types of attacks. It automatically generates attack prompts that bypass perplexity-based filters while maintaining a high attack success rate like manual jailbreak attacks. These prompts are interpretable and diverse, exhibiting strategies commonly used in manual jailbreak attacks, and transfer better than their non-readable counterparts when using limited training data or a single proxy model. We also customize \texttt{AutoDAN}'s objective to leak system prompts, another jailbreak application not addressed in the adversarial attack literature. %, demonstrating the versatility of the approach. We can also customize the objective of \texttt{AutoDAN} to leak system prompts, beyond the ability to elicit harmful content from the model, demonstrating the versatility of the approach. Our work provides a new way to red-team LLMs and to understand the mechanism of jailbreak attacks. less
By: Stefanos Koffas, Praveen Kumar Vadnala
We investigate the influence of clock frequency on the success rate of a fault injection attack. In particular, we examine the success rate of voltage and electromagnetic fault attacks for varying clock frequencies. Using three different tests that cover different components of a System-on-Chip, we perform fault injection while its CPU operates at different clock frequencies. Our results show that the attack's success rate increases with an... more
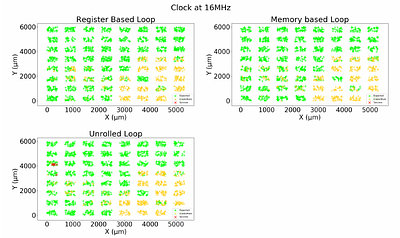
We investigate the influence of clock frequency on the success rate of a fault injection attack. In particular, we examine the success rate of voltage and electromagnetic fault attacks for varying clock frequencies. Using three different tests that cover different components of a System-on-Chip, we perform fault injection while its CPU operates at different clock frequencies. Our results show that the attack's success rate increases with an increase in clock frequency for both voltage and EM fault injection attacks. As the technology advances push the clock frequency further, these results can help assess the impact of fault injection attacks more accurately and develop appropriate countermeasures to address them. less
By: Maurantonio Caprolu, Savio Sciancalepore, Aleksandar Grigorov, Velyan Kolev, Gabriele Oligeri
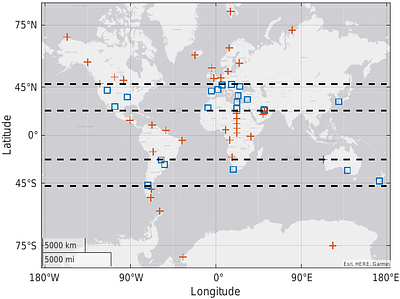
People Nearby is a service offered by Telegram that allows a user to discover other Telegram users, based only on geographical proximity. Nearby users are reported with a rough estimate of their distance from the position of the reference user, allowing Telegram to claim location privacy In this paper, we systematically analyze the location privacy provided by Telegram to users of the People Nearby service. Through an extensive measurement ... more
People Nearby is a service offered by Telegram that allows a user to discover other Telegram users, based only on geographical proximity. Nearby users are reported with a rough estimate of their distance from the position of the reference user, allowing Telegram to claim location privacy In this paper, we systematically analyze the location privacy provided by Telegram to users of the People Nearby service. Through an extensive measurement campaign run by spoofing the user's location all over the world, we reverse-engineer the algorithm adopted by People Nearby to compute distances between users. Although the service protects against precise user localization, we demonstrate that location privacy is always lower than the one declared by Telegram of 500 meters. Specifically, we discover that location privacy is a function of the geographical position of the user. Indeed, the radius of the location privacy area (localization error) spans between 400 meters (close to the equator) and 128 meters (close to the poles), with a difference of up to 75% (worst case) compared to what Telegram declares. After our responsible disclosure, Telegram updated the FAQ associated with the service. Finally, we provide some solutions and countermeasures that Telegram can implement to improve location privacy. In general, the reported findings highlight the significant privacy risks associated with using People Nearby service. less
By: Mengce Zheng
We point out critical deficiencies in lattice-based cryptanalysis of common prime RSA presented in ``Remarks on the cryptanalysis of common prime RSA for IoT constrained low power devices'' [Information Sciences, 538 (2020) 54--68]. To rectify these flaws, we carefully scrutinize the relevant parameters involved in the analysis during solving a specific trivariate integer polynomial equation. Additionally, we offer a synthesized attack illu... more
We point out critical deficiencies in lattice-based cryptanalysis of common prime RSA presented in ``Remarks on the cryptanalysis of common prime RSA for IoT constrained low power devices'' [Information Sciences, 538 (2020) 54--68]. To rectify these flaws, we carefully scrutinize the relevant parameters involved in the analysis during solving a specific trivariate integer polynomial equation. Additionally, we offer a synthesized attack illustration of small private key attacks on common prime RSA. less