RIPencapsulation: Defeating IP Encapsulation on TI MSP Devices
RIPencapsulation: Defeating IP Encapsulation on TI MSP Devices
Prakhar Sah, Matthew Hicks
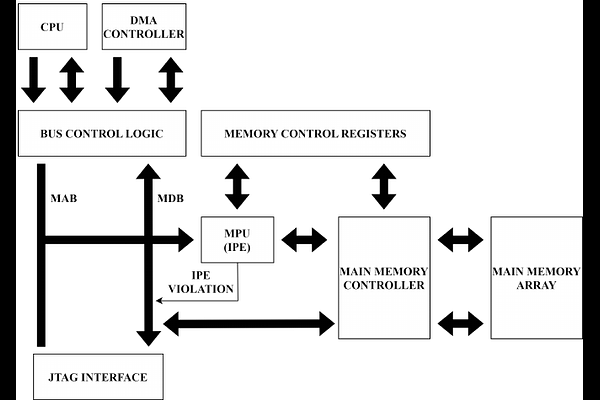
AbstractInternet of Things (IoT) devices sit at the intersection of unwieldy software complexity and unprecedented attacker access. This unique position comes with a daunting security challenge: how can I protect both proprietary code and confidential data on a device that the attacker has unfettered access to? Trusted Execution Environments (TEEs) promise to solve this challenge through hardware-based separation of trusted and untrusted computation and data. While TEEs do an adequate job of protecting secrets on desktop-class devices, we reveal that trade-offs made in one of the most widely-used commercial IoT devices undermine their TEE's security. This paper uncovers two fundamental weaknesses in IP Encapsulation (IPE), the TEE deployed by Texas Instruments for MSP430 and MSP432 devices. We observe that lack of call site enforcement and residual state after unexpected TEE exits enable an attacker to reveal all proprietary code and secret data within the IPE. We design and implement an attack called RIPencapsulation, which systematically executes portions of code within the IPE and uses the partial state revealed through the register file to exfiltrate secret data and to identify gadget instructions. The attack then uses gadget instructions to reveal all proprietary code within the IPE. Our evaluation with commodity devices and a production compiler and settings shows that -- even after following all manufacturer-recommended secure coding practices -- RIPencapsultaion reveals, within minutes, both the code and keys from third-party cryptographic implementations protected by the IPE.